#names. and then i uploaded it a second time but mobile doesn't let me format posts with multiple images anymore lmao
Explore tagged Tumblr posts
Text

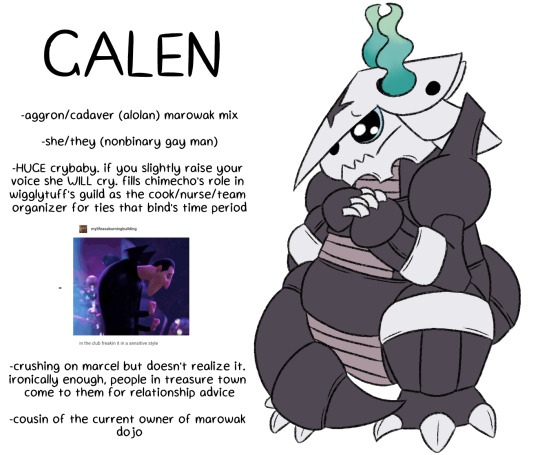
oh fuck here's some new guys. been wanting to make some more guild members beyond just shura for when kaira joins the guild and ngl i'm kinda obsessed with these guys rn despite them not being very important
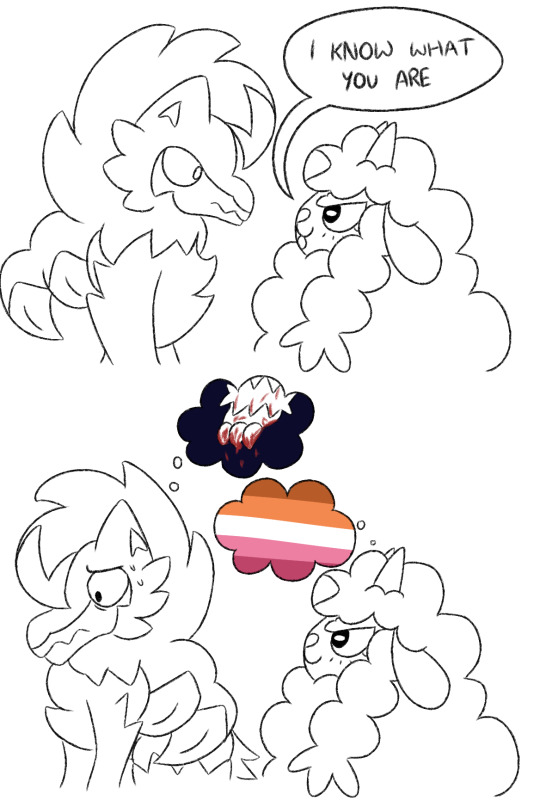
#pokemon#pkmnart#pkmn#pmd#pokemon mystery dungeon#pmd ocs#ties that bind#wooloo#oc: marcel#aggron#oc: galen#manectric#oc: shura#sorry for having to upload this three time. first i fucked up and forgot to edit their descriptions from when i hadn't decided on their#names. and then i uploaded it a second time but mobile doesn't let me format posts with multiple images anymore lmao#i die if there's any kind of mistake okay#anyway like i said the first two uploads don't worry about that bonus image okay? :)
20 notes
·
View notes
Text
How to download and play music for free on all your devices
Some folks don't know how to do this yet, but it's very easy to download files on your own devices to be able to access it whenever you want forever, without paying for it, without ads and without a need for internet connection.
(Since it's long, color code. Green for big themes, Blue(?) for notable topic changes, Red for direct links. I have put image descriptions where relevant)
//For downloads. There isn't a single place i can point to where you can download everything that exists ever for free. BUT. There are lots of ways all over the place.
For this post, i'll assume you use all the download sites from a computer, and move files to other devices using a USB to relevant-port cable, but i think most work from mobile ? I haven't checked that. If you want to sort your files neatly i highly advise doing it from a PC anyway.
-> For Spotify specifically, i very recently found spotdownloader, you can put in a spotify link for a song, album or playlist and generate a download link. It gives high quality mp3s, with full metadata. Just know that the site seems to not do much when you click download, just let it sit for a bit and it will do its thing, slowly yes but eventually the files will appear in your download folder. There are instructions on the site (including for how to use a script to directly add a download button to spotify) so no need for me to explain much more.
(as a test for this post, i downloaded all of the Arcane S2 songs. It's not exactly perfect, I think the audio doesn't always directly come from spotify, so sometimes you might get some minor differences, like a few seconds more in the beginning or the end (for examples, i have one song with the netflix logo sound at the end, and another one with sound from a clip from arcane at the beginning), but nothing major)
-> A good place to start for other sources is cobalt.tools. You can paste links to youtube or even audio files that are directly on tumblr. The defaults setting are a bit weird, i personally go and set it to have a good automatic title and (this is important !!!) get the audio quality up to at least 256kb/s, otherwise sound quality is kinda bad (by defaults it sits at 128kb/s and it's a bit crunchy)

Since you can find most music on youtube, this is great for downloading individual tracks. It can also save video and audio files from other sources, including tiktok or soundcloud, but not spotify
It struggles with very long videos though, even when downloading just the audio (you just select "audio" on the main menu for that), i've tried with a 45 minutes video just to see, i got 9 minutes of video and 33 minutes of audio, not the entire video (not sure what's up with that, it's perfect with shorter stuff though)

Since you can find most music on youtube or soundcloud, with a bit of patience you can easily get almost whatever you want using this.
Up until very recently i had a working addon to download from youtube, but right now it doesn't work and I haven't found a working replacement yet.
-> Websites like Video Game Music Downloads are very good - and despite the name, not exclusively for video games(there is an anime section), but mostly - it's free to download tracks individually, they have full metadata. (You can access the one click album downloads by either donating - whichever amount and you're good to go for a set time -, uploading something yourself, or giving a referral link to someone else)
-> Some artists on bandcamp have stuff that you can directly download for free, but that's rare so you can check whether that's the case or not but don't count on it
//Now for reading them, just in case. Most computers have an included audio file reader, but i always recommend getting VLC, which is lightweight and can do everything you need with sometimes easier access to different options, and is compatible with every OS out there as well as most audio file formats. An important one, especially if you want to get your music on your phone, is metadata.

You access this screen by opening a file with VLC, accessing the track list screen (on the bottom or the left, it might not open by default), then right-clicking on the track and selecting Informations (or something similar i couldn't access VLC in english right now).
The most important stuff you might want to edit are the Title, Artist and Album fields, as those are the ones music readers are most likely to look at. I sadly did not find a way to mass edit these. On windows (up to win 10 at least, I did not test the later ones) you can also change these by right-clicking on files and accessing their properties, there is a metadata screen that you can edit, and if memory serves you can do that with several files selected at once.
VLC has a library section too, in which you can organise your songs, albums and everything if you want to. Personally I never used it, i prefer to rely on good old-fashioned folders to sort everything, but that's me and my habit of listening to albums rather than playlists so it can be useful, just not my thing personally.
//Now to read audio files on your phone !!
First, check your integrated music app as it normally should have fatures to read local music files, but it is important to note that you might not natively have an app that can easily read music locally. Which is terrible, i know, but I know that from first-hand experience (my current phone came with Google Play Music installed, which could read local files but was deprecated in favour of Youtube Music which cannot do that, so I had to get another app).
So just in case, here's a link to this app, which can read local files and sort them by artist, albums or even custom playlists. Comes with varying widgets you can put on your main menu for quick use, etc. It has ads, but not all the time and only in the UI, it never interrupts your music to play an ad. Might not be the best one, there are several others out there, and I don't have another example for Apple phones, sorry for that.
A thing to note : it will sort music based on metadata, which is why I deemed it important to edit downloaded music using VLC before putting said files on your phone. If you did not do it, there is a UI to edit metadata in the app, i personally find it a bit less practical but that might be a personal bias, technically it's fine. Also you can change album covers using said app, but you need to store the images on your phone too (there is a button to help find relevant album covers using the song titles and artist names, it just links to google images but it works)
@dog-with-anxiety here you go. I wanted to be extra precise just in case, and feel free to share the info.
#music download#i've always been a big advocate of getting your music stored somewhere but i get that the info on how to actually do that#especially if you aren't rich enough to pay for every single album-#isnt exactly obvious or the easiest to find if you dont know what to search for#so here#this is not an exhaustive list as that would probably be impossible#but i wanted to share at least the options i personally use. which are very versatile overall#without needing to resort to the old unreliable “google this album hard enough and you might find a link that's not super shady” technique
6 notes
·
View notes
Text
Catch
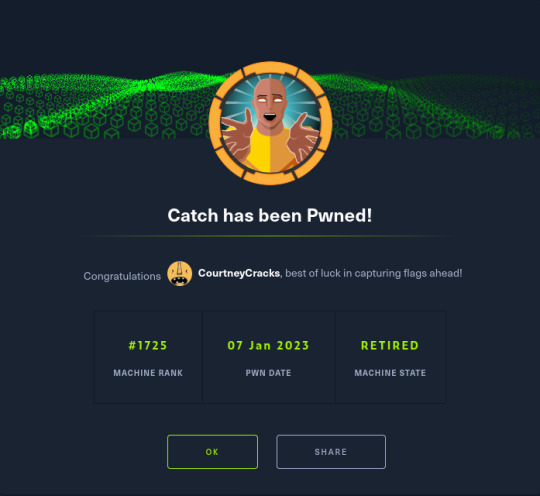
So over the last few weeks I've been working on Catch. With work and the festive period I haven't had a lot of time; I finally got the opportunity to finish it last night. :)
It has a medium rating but I wouldn't say it's due to the initial foothold and privilege escalation being difficult- it's more due to there being a couple of rabbit holes (all of which I fell into for a period!)

Enumeration
As always, a port scan kicks off the process. Unfortunately I can't show the output of the port scan as during the time I switched laptops and I'm too lazy to power my old one on. xD However, the results were roughly as follows:
Port 80: HTTP (Catch Global Systems main page)
Port 3000: Gitea(?)
Port 5000: Lets Chat(?)
Port 8000: Cachet status page system
Port 80 was the first location I checked. You're greeted with what appears to be Catch's main application:
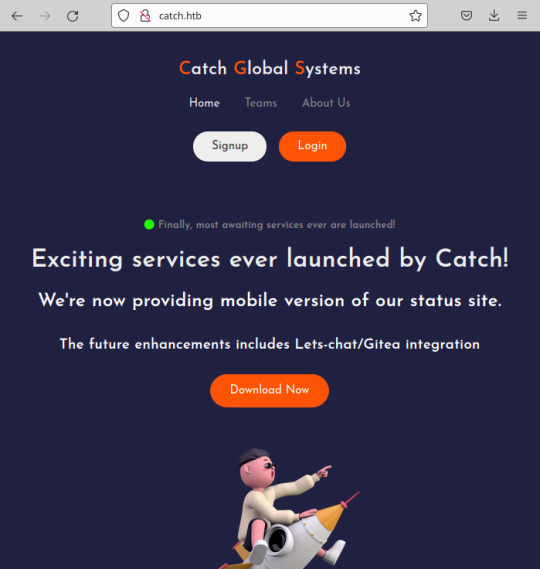
The signup/login functionality isn't present; I did notice the ability to download a file. The file that downloads is an apk.
For those that are unfamiliar with mobile applications, apk is one of the file formats for an Android mobile application which uses XML and Java. Having a little experience with mobile applications, my first thought was to decompile the apk and check for any hidden hardcoded secrets, usually stored in strings.xml.
To decompile the apk, I used apktool.
$ apktool d catchv1.0.apk
This decompiles the apk to near it's original form and places the resulting files in ./catchv1.0/. From here, I viewed ./res/values/strings.xml and found 3 potentially usable tokens for other applications:
$ grep token catchv1.0/res/values/strings.xml <string name="gitea_token">b87bfb6345ae72ed5ecdcee05bcb34c83806fbd0</string> <string name="lets_chat_token">NjFiODZhZWFkOTg0ZTI0NTEwMzZlYjE2OmQ1ODg0NjhmZjhiYWU0NDYzNzlhNTdmYTJiNGU2M2EyMzY4MjI0MzM2YjU5NDljNQ==</string> <string name="slack_token">xoxp-23984754863-2348975623103</string>
Foothold
With these in hand, I started with Lets Chat at random. Lets Chat is an open-source chat application utilizing a REST api. With it being open-source, it didn't take long at all to find how to use the discovered token:
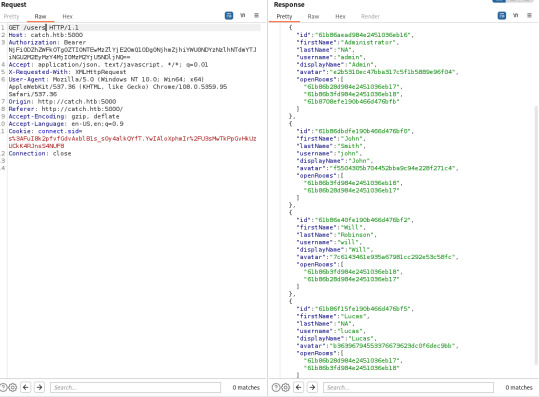

As you can see, a password for John is viewable in one of the chat rooms. This grants you access to another one of their applications called Cachet- open-source yet again.
Cachet is the last stop before system access; admittedly this is where I fell rabbit hole 1 as I did spend some time trying to use the gitea_token, more out of curiosity than anything. After spending some time on this, however, I gave up and focused on Cachet.
As it turns out, the version of Cachet in use had two pubicly known vulnerabilities related to interaction with the application's dotenv file. One allowed you to leak values set in dotenv while the other allowed you to add new values to dotenv which could be used to achieve remote command execution. This is done by hosting a redis server, altering the dotenv file to make the application use your hosted redis server as a session driver and finally changing the value of the session key after the initial connection to a payload generated by phpggc. Better detail off this is given here.
I did spend some time playing around with the RCE vulnerability here, more out of interest as I haven't had any experience with Redis prior to this and it took me a while to get RCE working as the video doesn't explicitly show the process step-by-step.
Originally, I was getting the token from the source code in the application, adding this as a key with the phpggc payload as the value and then altering the dotenv file to connect to my Redis Server. As the RCE occurs when the client connects the second time and reads the value from the original session token, this didn't work.
I did eventually get this working, uploaded a PHP web shell and upgraded this to a reverse shell; this ultimately proved to be a waste of time as you end up in a Docker instance with no ability to break out of it!
With a heavy heart, I turned to the second vulnerability and leaked the database password from the dotenv file. This grants us access to the server through SSH as WIll.
Privilege Escalation
Privilege escalation was actually quite easy! Some simple enumeration reveals the presence of world-writeable directory /opt/mdm/apk_bin. In /opt/mdm, there is a Bash file verify.sh.
verify.sh is used to verify the legitimacy of apks uploaded to apk_bin and is executed as part of a cronjob which is executed as root. While references to verify.sh cannot be directly found, there is reference to 'check.sh' in the root directory in running processes (netstat -ano.)
The interesting lines of the script are here:
app_check() { APP_NAME=$(grep -oPm1 "(?<=string name=\"app_name\">)[^<]+" "$1/res/values/strings.xml") echo $APP_NAME ...
The function app_check is taking the app_name from strings.xml and echoing it back with no form of mitigation against command injection. For example, wrapping the variable name with ${} would have prevented this vulnerability being exploitable as this would have specified that only variable expansion was expected- the app name would have been echoed back as a string and not interpreted as a literal Bash command.
I tested this first by simply making the app name 'Catch; touch /opt/mdm/heuheu' and uploading it using python -m SimpleHTTPServer on my end and curl on Catch's end which achieved the expected outcome.
I did this with APK Editor Studio after encountering some errors trying do manually decompile and then recompile with apktool. Note that you also need to create a key for signing the APK as verify.sh uses jarsigner to verify this.
will@catch:/opt/mdm/apk_bin$ ls -al .. total 16 drwxr-x--x+ 3 root root 4096 Jan 6 21:55 . drwxr-xr-x 4 root root 4096 Dec 16 2021 .. drwxrwx--x+ 2 root root 4096 Jan 6 22:03 apk_bin -rw-r--r-- 1 root root 0 Jan 6 21:55 heuheu -rwxr-x--x+ 1 root root 1894 Mar 3 2022 verify.sh
From here, I went old school and just made /etc/passwd fully accessible by everyone before changing root's password to 'mwaha'
Generating the password:
$ openssl passwd mwaha KW56XEY7wxZuU
Where the password is added in /etc/passwd:
root:KW56XEY7wxZuU:...
There you go. ^-^
#hackthebox#hacking#android apk#apktool#command injection#redis server#dotenv#cachet#lets chat#gitea#cronjob#web shell#reverse shell#ssh#docker#open source
20 notes
·
View notes